Content
Protecting Curve Community with CUBE3.AI (and a DM?)
Vyper’s reentrancy vulnerability highlights another zero-day event that further illustrates the need for real-time security tools in web3. Dependencies beyond your control (eg compilers) can become attack vectors that compromise protocol and community security. Audits, bug bounties and threat simulation are critical tools in the initial security stack, but there is still a massive security gap in web3, post deployment. CUBE3.AI is providing free security tools for web3 communities like Curve, as a public good.
The calls for web3 “AI firewall” are more warranted than ever, and that is exactly why CUBE3.AI was created. Learn more about who we are and why we exist as a real-time transaction security layer for web3. Our advanced machine learning models flag threats, fraud, and compliance risk and our Runtime Application Self-Protection (RASP) blocks exploits before they resolve on-chain.
Proactive Protection Prevents Postmortems
The reentrancy losses observed in the past week across the Curve ecosystem highlight the critical need for real-time detection and protection for deployed contracts and protocols.
Since the root cause of Curve pool vulnerabilities are not a contract bug but the Vyper compiler (v0.2.15, 0.2.16 and 0.3.0), there are still vulnerable contracts out there. There have been superb postmortems on the topic (for example, here and here) detailing the recent Vyper/Curve events. Instead of focusing on how much was drained from pools, we want to identify tools to mitigate risk and the role of community coordination.
Free Security Tools for Web3
Real-time transaction security gives the community an advantage against cyber criminals and hackers. We’re providing the core of our Detect and Manage products at no cost to the community as a public good. Input any address or contract you want to protect and/or track activity. It can alert projects and teams when concerning data is uncovered and prevent everyone from getting rekt.
Sign up to monitor any contract (yours or any community member’s) and get real-time activity alerts, including blocked malicious transactions, when you use our Protect product.
For example, a Curve exploiter address can be tracked using CUBE3’s Monitor tool:
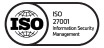
CUBE3.AI ML detection identified the attacker contracts and flagged addresses as high risk:
- JPEGd_69 Exploit Tx Hash
- Frontrunner Address (JPEGd_69 Exploiter):
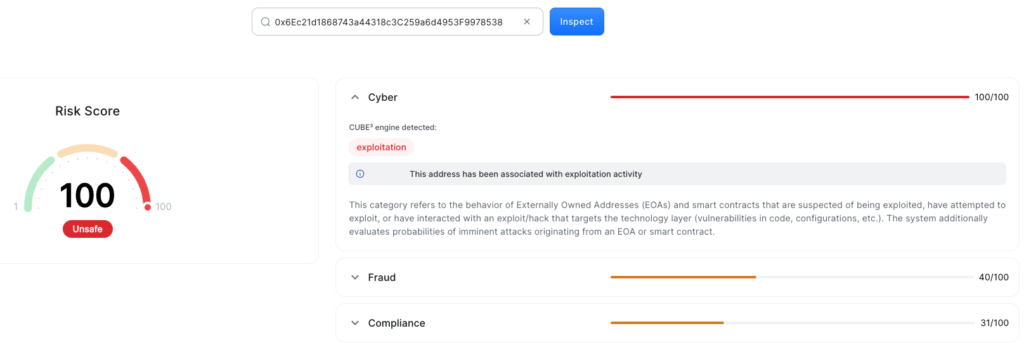
- CurveFinance AlchemixFi Exploit Tx Hash
- AlchemixFi Exploiter Address drained $20.5M, but $11.5M was recovered:
Real-time Security = Code + Community
Reducing the $70 million Curve pools losses is a combination of real-time transaction security, combined with community relationships. CUBE3.AI built a web3 security platform that not only monitors and alerts of risks, but blocks threats before they resolve on-chain. However, code alone can’t protect web3. Every layer of the smart contract security stack plays a role in making web3 safer.
We have a responsibility to alert the community to vulnerabilities and threats, while balancing public communications with private discretion where needed. We want to inform the broadest range of developers, founders and contributors of vulnerabilities without attracting the attention of bad actors.
However, contacting vulnerable projects is difficult if they’re not using our tools. Some community led solutions are emerging, like Seal 911.
DM us your addresses, links to your bounty programs and contact info for zero-day alerts BEFORE A THREAT IS DETECTED. Transparent communication is a group effort to preserve and protect the web3 community. We sincerely hope you reach out, so we can build a relationship regardless of whether you use our platform.
Take action today by building knowledge and relationships with runtime web3 security platforms and teams like ours. Join our Telegram Group / Twitter @CUBE3AI and contribute your questions, concerns and ideas.
As community leaders at Bankless observe, people are the true “layer zero” of web3. The community is responsible for the health and progress of the entire ecosystem.
Join us as we launch our Detect, Protect and Manage products for a safer, more decentralized world.

 CUBE3.AI
CUBE3.AI


 Einaras Gravrock
Einaras Gravrock

 Sarunas Matulevicius
Sarunas Matulevicius
 Attila Marosi-Bauer
Attila Marosi-Bauer


 Tamás Kelemen
Tamás Kelemen